My 3 Big Predictions for Security in 2015
2014 was an interesting year to be working in security. The bad guys showed us that they were still capable of capturing the headlines and that even technocentric companies, presumably with ranks full of security savvy employees and managers weren't safe (if they can't stay secure, who can?). Their links to organised (and more traditional) crime were highlighted through a series of enormous breaches, typically designed to steal credit cards and PII. These attacks found success with huge retailers and restaurant chains, and even banks. We became aware of 'regin', a form of advanced and presumably state sponsored malware which could exist within the registry of an infected host, sort of like a 'cyber ghost'. It may have been been doing the rounds (undetected) for almost a decade according to one vendor. The internet continued to move into the home and closer to the heart through the rise of home automation and a general increase in the number of 'smart' devices and the release of more accessible wearable tech.
Overall, all this has contributed to what has felt like a growing sense of fear, confusion and helplessness about the topic of security. The public's perception of the internet and what it represents along with what is popularly referred to as 'cyber security' remains one of ignorance and fear. On the one hand, the internet is fully accepted into the lives of many, seen as essential and treated like any other utility, like electricity or water. As more things become internet enabled and data-hungry the number of consumers and use-cases for consumption is set to continue rising. On the other hand, the internet, its architecture and governance, and what constitutes good security practice, remains as mis-understood as it ever was. From a users perspective, they simply want to consume the internet like any other utility and their personal responsibilities towards doing this in a safe way is typically to select a good password, and that's all. We (as security professionals) need to change this if we're to drive improvement.
Education is the best defense, for our users, our developers and our architects. As companies, we need to integrate security into solution design and architecture (from day 0) and push for change if its missing. We need to take things back to basics, adopt security models (such as the SANS20 Critical Security Controls) that are geared towards improving actual security and not merely demonstrating compliance. We need to push for risk acceptance (formally) and hold people accountable for designing secure solutions and hold people accountable for when they fail. We need to move away from the endpoint security model and start looking to secure and monitor our networks as they are by far our biggest asset and ultimately facilitate access to our data, the thing we are trying to protect. We need to improve user awareness of all the other security considerations that aren't a password. They need to understand why they need to patch, they need to understand why they shouldn't open that invoice they've just received in their inbox unexpectedly, they need to understand that Microsoft don't call you at home to troubleshoot printers, and they need to understand what to do and who to call when they make any of those mistakes.
Education is the best defense, for our users, our developers and our architects. As companies, we need to integrate security into solution design and architecture (from day 0) and push for change if its missing. We need to take things back to basics, adopt security models (such as the SANS20 Critical Security Controls) that are geared towards improving actual security and not merely demonstrating compliance. We need to push for risk acceptance (formally) and hold people accountable for designing secure solutions and hold people accountable for when they fail. We need to move away from the endpoint security model and start looking to secure and monitor our networks as they are by far our biggest asset and ultimately facilitate access to our data, the thing we are trying to protect. We need to improve user awareness of all the other security considerations that aren't a password. They need to understand why they need to patch, they need to understand why they shouldn't open that invoice they've just received in their inbox unexpectedly, they need to understand that Microsoft don't call you at home to troubleshoot printers, and they need to understand what to do and who to call when they make any of those mistakes.
The alternative is that we design a system that does all this inherently, but I don't see that happening any time soon.
With the state of thing being as they are I predict 2015 will bring more of the same...
1 . Detection of more state sponsored, military grade Malware
I'd like to take this opportunity to express a huge amount of thanks and gratitude to the community. The response and efforts of so many stand out but I'd like to extend specific thanks to Conrad, Brad, Leigh, Malekal, the team at Malwr, and everyone involved in CiSP via CERT-UK for their continued collaborative efforts.
2 . Breaches. Lots of Breaches.
3 . Attacks on (and from) the Internet of Things (IoT)
In regards to the Internet of Things (IoT) I have just this to say - we're just not ready...
Like all consumer driven technological movements, the focus is on designing products that are desirable and functional first with security appearing somewhere (much) lower on the list of priorities. I predict that we'll see more products entering the market (a new market) which will be plagued by all the same problems embedded devices face today. Failures to provision and manage patching (and technical vulnerability management in general), weaknesses in (or a complete lack of) access control considerations and concerns about surveillance potential will probably form the root cause for many security concerns around IoT devices and systems in the years to come. I'm confident, as more IoT devices make it online that we'll see them falling to vulnerabilities and then contributing to the distributed architecture employed in activities such as DDoS attacks and malware distribution.
Its taken almost a generation to get consumer endpoint and awareness to the place they're in now, and that is far from perfect. Adding refrigerators, televisions and maybe even automobiles to the same 'scope' is a big ask...
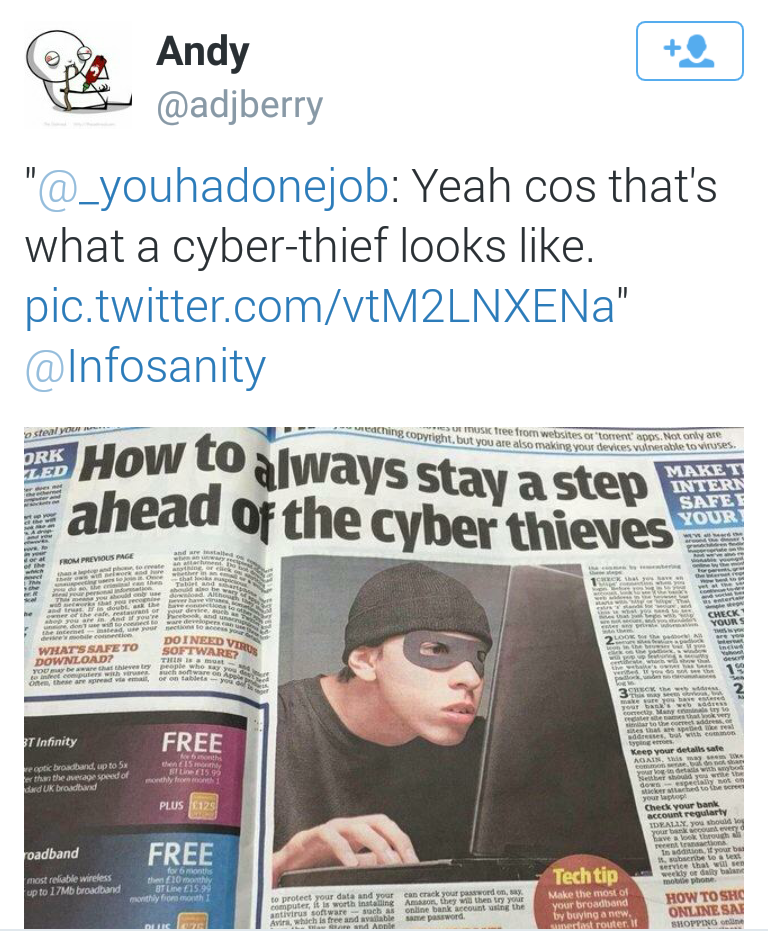
Bonus . A continuation in the use of ridiculous photos in security press articles
You know the ones I mean. Hooded figures crouching over laptops in the dark, balaclava clad cyber terrorists reaching out through the screen to grab your loved ones or masked anarchists threatening to topple democracy and capitalism outright...
 |
| Nailed it. |







